DevSecOps with WINTrio
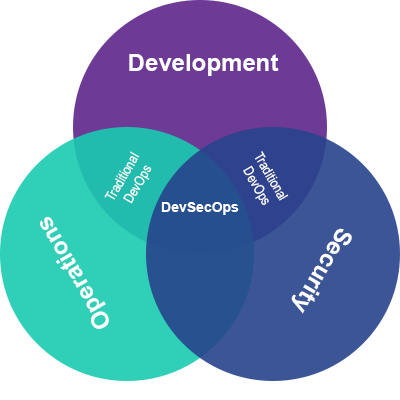
DevSecOps is all about ensuring data security. It focuses on data and systems protection and doing what is necessary to defend against attackers. WINTrio uses simple tools that ensure everyone takes an active part in protecting information. We provide training and assistance so that employees are more likely to identify phishing, malware, or other penetration attempts.
Our IT and Cybersecurity experts help you advance to a better security posture. We work with you to identify security flaws in your systems and implement a plan to close the gaps. Then together we discuss areas of vulnerability and ways to mitigate them
Security breaches and data loss disrupts operations and seriously damages an organization’s reputation. WINTrio uses DevSecOps to help reduce your organization’s risk.
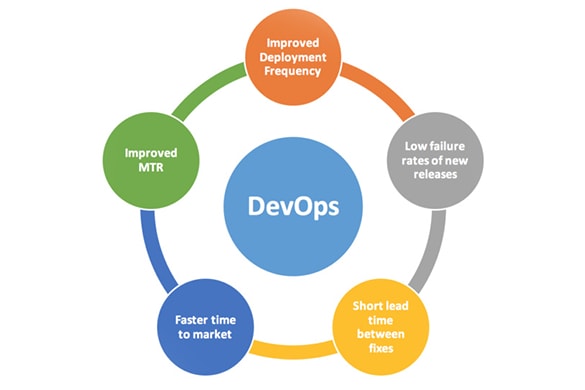
To successfully implement a DevSecOps service, you can count on WINTrio to provide static, dynamic analysis, penetration testing, dependency scanning, source code integrity, and code signing. Our goal is to provide fast DevSecOps feedback with prompt notifications when potentially insecure changes are made. WINTrio experts ensure quick detection and correction of security problems, enabling the prevention of future errors.
The WINTrio Advantage
WINTrio brings people, process, and technology together where organizational change, cultural transformation, and emerging operational environments require changes to IT infrastructure or data management. Our Technology and Agile Process experts provide support at both the architectural and implementation levels. We make your vision a reality by overcoming complex systems integration challenges both internal and external to your organization. We help you manage technology changes from requirements planning through to architecture development, testing, deployment and maintenance. Our focus is on achieving results, reducing risk, and ensuring quality.
DevSecOps and Cyber Engineering
- Complete automation of CI/CD pipelines by encompassing the security without any disruption
- Security Architecture
- Computer Incident Response
- Vulnerability Management
- Security Assessment and Authorization (A&A)
- Continuous Monitoring and Real-Time Assessments
- Penetration Testing Ethical Hacking
- Tooling Expertise: WebInspect, Nessus, Fortify, DBProtect, Xacta, AppScan, and Nipper











